Chapter 13. Basic Firewall Configuration
Just as a firewall in a building attempts to prevent a fire from spreading, a computer firewall attempts to prevent computer viruses from spreading to your computer and to prevent unauthorized users from accessing your computer. A firewall exists between your computer and the network. It determines which services on your computer remote users on the network can access. A properly configured firewall can greatly increase the security of your system. It is recommended that you configure a firewall for any Red Hat Linux system with an Internet connection.
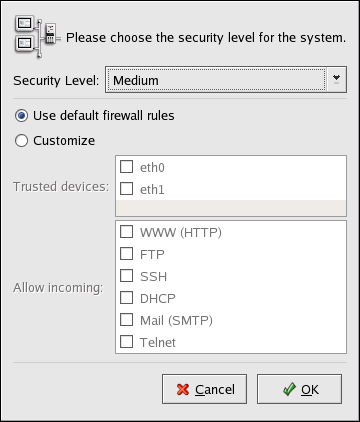
13.1. Security Level Configuration Tool
During the Firewall Configuration screen of the Red Hat Linux installation, you were given the option to choose a high, medium, or no security level as well as allow specific devices, incoming services, and ports.
After installation, you can change the security level of your system by using the Security Level Configuration Tool. If you prefer a wizard-based application, refer to Section 13.2 GNOME Lokkit.
To start the application, select Main Menu Button (on the Panel) => System Settings => Security Level or type the command redhat-config-securitylevel from a shell prompt (for example, in an XTerm or a GNOME terminal).
Select the desired security level from pulldown menu.
- High
If you choose High, your system will not accept connections (other than the default settings) that are not explicitly defined by you. By default, only the following connections are allowed:
DNS replies
DHCP — so any network interfaces that use DHCP can be properly configured
If you choose High, your firewall will not allow the following:
Active mode FTP (passive mode FTP, used by default in most clients, should still work)
IRC DCC file transfers
RealAudio™
Remote X Window System clients
If you are connecting your system to the Internet, but do not plan to run a server, this is the safest choice. If additional services are needed, you can choose Customize to allow specific services through the firewall.

Note If you select a medium or high firewall, network authentication methods (NIS and LDAP) will not work.
- Medium
If you choose Medium, your firewall will not allow remote machines to have access to certain resources on your system. By default, access to the following resources are not allowed:
Ports lower than 1023 — the standard reserved ports, used by most system services, such as FTP, SSH, telnet, HTTP, and NIS.
The NFS server port (2049) — NFS is disabled for both remote severs and local clients.
The local X Window System display for remote X clients.
The X Font server port (by default, xfs does not listen on the network; it is disabled in the font server).
If you want to allow resources such as RealAudio™ while still blocking access to normal system services, choose Medium. Select Customize to allow specific services through the firewall.

Note If you select a medium or high firewall, network authentication methods (NIS and LDAP) will not work.
- No Firewall
No firewall provides complete access to your system and does no security checking. Security checking is the disabling of access to certain services. This should only be selected if you are running on a trusted network (not the Internet) or plan to do more firewall configuration later.
Choose Customize to add trusted devices or to allow additional incoming services.
- Trusted Devices
Selecting any of the Trusted Devices allows access to your system for all traffic from that device; it is excluded from the firewall rules. For example, if you are running a local network, but are connected to the Internet via a PPP dialup, you can check eth0 and any traffic coming from your local network will be allowed. Selecting eth0 as trusted means all traffic over the Ethernet is allowed, put the ppp0 interface is still firewalled. If you want to restrict traffic on an interface, leave it unchecked.
It is not recommended that you make any device that is connected to public networks, such as the Internet, a Trusted Device.
- Allow Incoming
Enabling these options allow the specified services to pass through the firewall. Note, during a workstation installation, the majority of these services are not installed on the system.
- DHCP
If you allow incoming DHCP queries and replies, you allow any network interface that uses DHCP to determine its IP address. DHCP is normally enabled. If DHCP is not enabled, your computer can no longer get an IP address.
- SSH
Secure SHell (SSH) is a suite of tools for logging into and executing commands on a remote machine. If you plan to use SSH tools to access your machine through a firewall, enable this option. You must have the openssh-server package installed in order to access your machine remotely, using SSH tools.
- Telnet
Telnet is a protocol for logging into remote machines. Telnet communications are unencrypted and provide no security from network snooping. Allowing incoming Telnet access is not recommended. If you do want to allow inbound Telnet access, you must have the telnet-server package installed.
- WWW (HTTP)
The HTTP protocol is used by Apache (and by other Web servers) to serve webpages. If you plan on making your Web server publicly available, enable this option. This option is not required for viewing pages locally or for developing webpages. You must have the apache package installed if you want to serve webpages.
Enabling WWW (HTTP) will not open a port for HTTPS. To enable HTTPS, specify it in the Other ports field.
- Mail (SMTP)
If you want to allow incoming mail delivery through your firewall, so that remote hosts can connect directly to your machine to deliver mail, enable this option. You do not need to enable this if you collect your mail from your ISP's server using POP3 or IMAP, or if you use a tool such as fetchmail. Note that an improperly configured SMTP server can allow remote machines to use your server to send spam.
- FTP
The FTP protocol is used to transfer files between machines on a network. If you plan on making your FTP server publicly available, enable this option. The vsftpd package must be installed for this option to be useful.
Click OK to activate the firewall. After clicking OK, the options selected are translated to iptables commands and written to the /etc/sysconfig/iptables file. The iptables service is also started so that the firewall is activated immediately after saving the selected options.
 | Warning |
|---|---|
If you have a firewall configured or any firewall rules in the /etc/sysconfig/iptables file, the file will be deleted if you select No Firewall and click OK to save the changes. |
The options selected are also written to the /etc/sysconfig/redhat-config-securitylevel file so that the setting can be restored the next time the application is started. Do not edit this file by hand.
To activate the iptables service to start automatically at boot time, refer to Section 13.3 Activating the iptables Service for details.